Reports
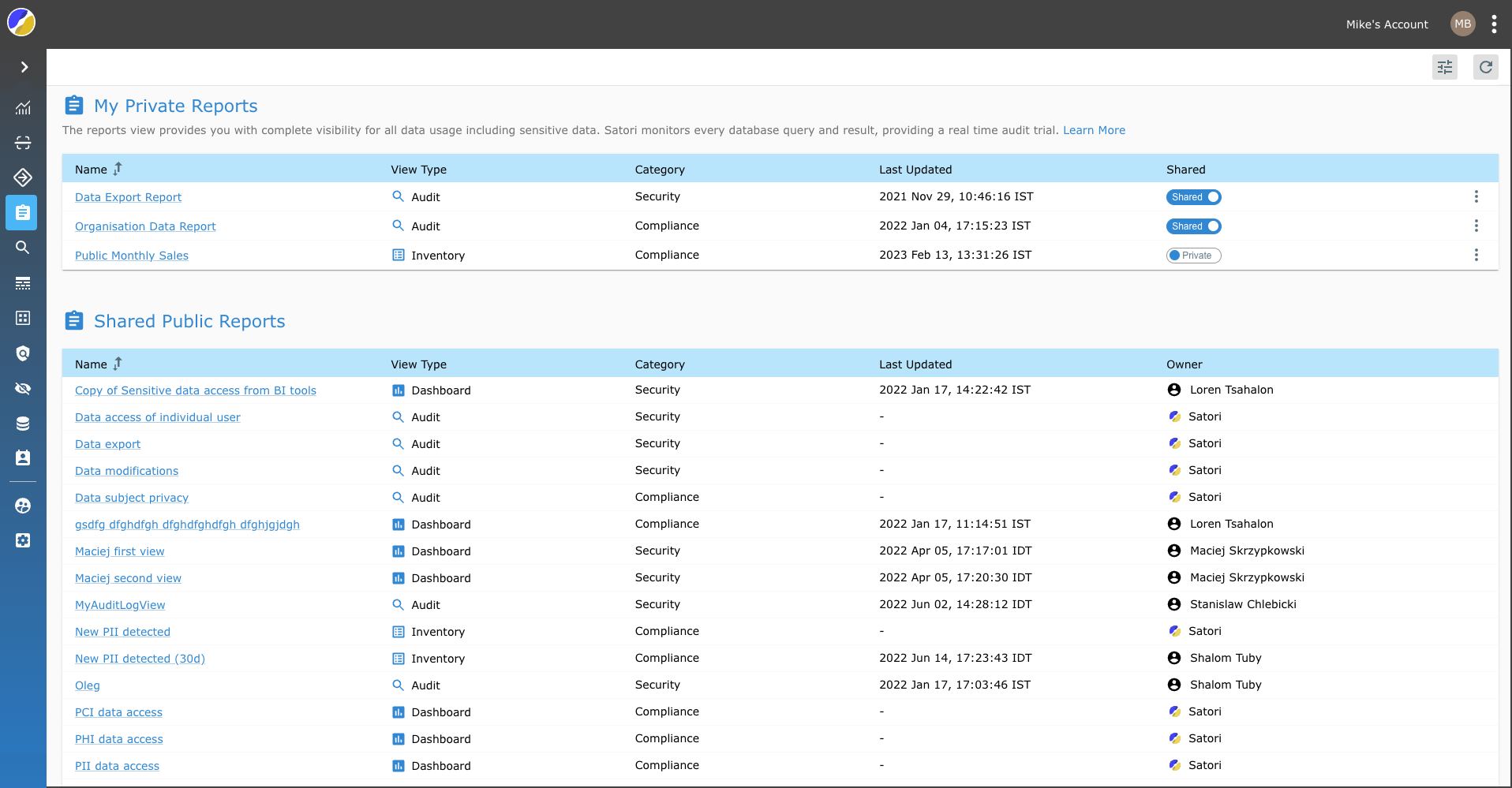
The reports view provides you with complete visibility for all data usage including sensitive data. Satori monitors every database query and result, providing a real time audit trail.
Predefined Out-of-the-Box Reports
Satori provides you with predefined reports that allow you to easily identify data export attempts, malicious access to individual user records and new PII locations.
Shared Reports
Satori has created a set of preconfigured shared reports designed to cover a range of day to day use cases including, potential threat and security data breach scenarios common to most organizations.
The following list describes the available reports and provides examples of the types of threats they enable you to monitor.
- Data Access of Individual User Report - This report enables you to monitor data access of potential insider threats within your organization. (Including the use of DML queries).
- Data Export Report - This report can help you monitor individuals that carry out large DB export transaction such as departing employees. (Including the use of DML COPY queries).
- Data Modification Report - This report helps expose individuals that have altered, changed or manipulated data within your organization. (Including the use of DML queries).
- Data Subject Privacy Report - This report highlights individuals who have accessed sensitive information for specific data subjects. (specific users).
- New PII Detected Report - This report exposes new personal identifiable information tags that have been detected in your organization by Satori. (Including all PII instances in the data inventory discovered in the last week).
- PCI Data Access Report - This report highlights individuals that have accessed payment card information data in your organization. Including all recent access to PCI across all data stores.
- PHI Data Access Report - This report highlights individuals that have accessed personal health information data in your organization. Including all recent access to PHI across all data stores.
- PII Data Access Report - This report highlights individuals that have accessed personal identifiable information data in your organization. Including all recent access to PHI across all data stores.
- Sensitive Data Access from BI Tools Report - This report highlights individuals that have accessed sensitive data via BI tools in your organization. (Includes all access of BI tools to all instances of sensitive data based on Satori’s tagging).
Report Privacy Types
You can create two types of reports, private reports for your eyes only and public reports that are visible to all of the users you have defined for a specific account.
How to Generate Reports
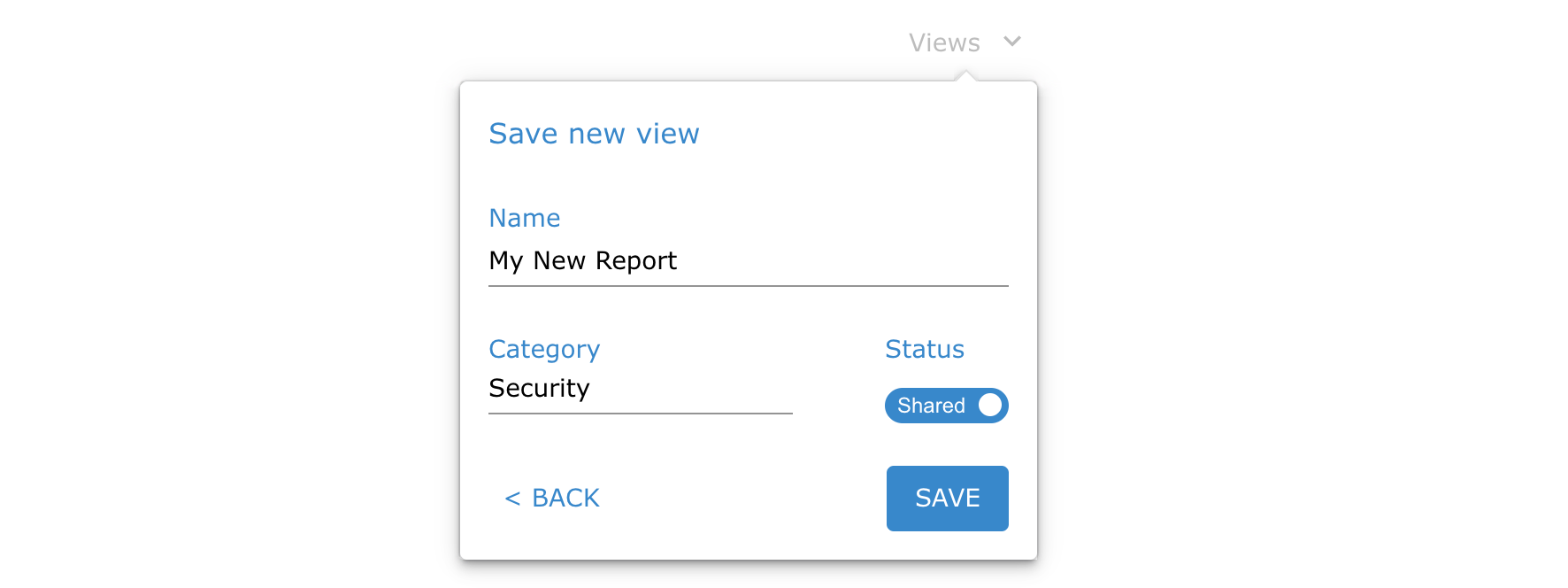
You can generate reports from the Dashboard, Audit Log, Data Inventory views. Create a report by performing the following steps:
- Go to one of the perviously mentioned views and click the VIEW button.
- Click the SAVE button.
- Provide a name for the report (view).
- Select the relevant category.
- Select whether the report is private or public.
- Click the SAVE button.
- Go to the Reports view to access the report.