User Directory
The User Directory enables Satori administrators to define user groups in Satori based on existing users, identity provider groups and data store groups.
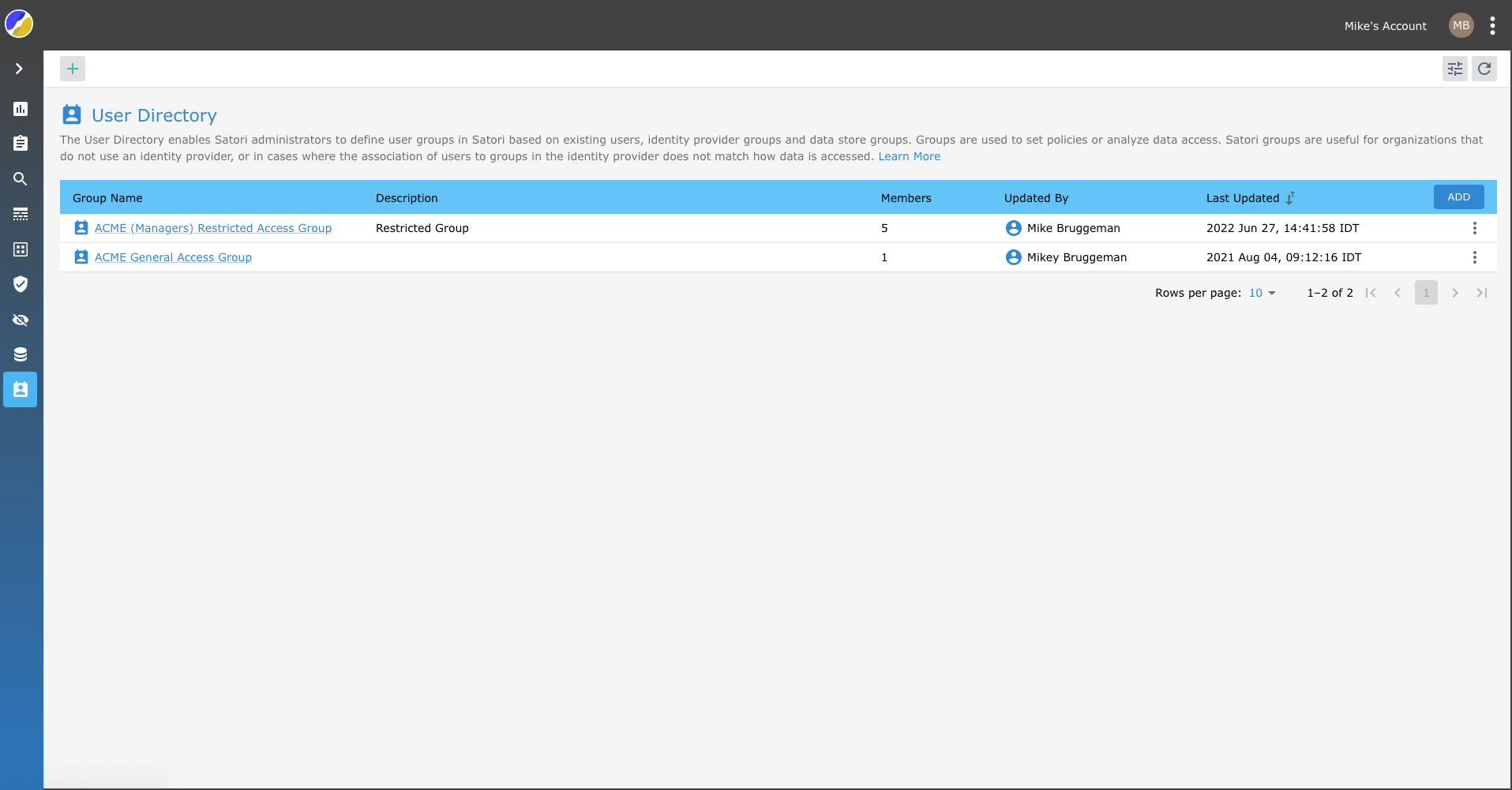
Groups are used to set policies or analyze data access. Satori groups are useful for organizations that do not use an identity provider, or in cases where the association of users to groups in the identity provider does not match how data is accessed.
Using Groups
For example; If an organization has created a dataset for a project and is accessed by the following employees types:
- A team of software engineers are assigned to an Okta group called ProjectXEngineers
- A python script that uses the username project_x_billing_job
- Several analysts using a BI tool that uses the username project_x_bi
Policy Enforcement
To enforce the same policy on all these users and to be able to easily produce a report on the data access of these users, create a Satori group named Project X and add the following members:
- Okta group
ProjectXEngineers project_x_biandproject_x_billing_jobusernames
Group Hierarchy
To enable organizations to create a hierarchy model for groups, Satori groups can be added as members of other Satori groups, under the following constraints;
- Group Hierarchy - A maximum of 10 levels.
- Avoid Creating Loops - A group cannot be added as a member of itself, indirectly (creating a loop).
Creating Satori Groups
To create a Satori group go to the User Directory view, click the "Add" button and then provide a name for the group. A group can contain the following members:
- Usernames - any user that is used to access a data store
- Identity Provider Groups - Okta, AzureAD or others
- Snowflake roles
- Other Satori groups
Define Policies using Satori Groups
Organizations can enforce policies on Satori groups the same way policies are enforced on users or identity provider groups. This is performed by using the identity.directory.group tag. For example, the following policy will alert you on access to PII data by members of the Project X team:
- name: "Project X PII"
action: alert
identity_tags:
- identity.directory.group::e36cde67-6048-4ab3-b6f5-22b0aa311f80
data_tags:
- c12n.pii
priority: 1